Ahmedabad Police Capture Illegal Immigrant Linked to Nationwide Bomb Threat Emails

Synopsis
Key Takeaways
Ahmedabad, March 5 (NationPress) The police in Ahmedabad have apprehended an illegal immigrant living in West Bengal for allegedly being part of a network responsible for sending bomb threat emails to various institutions, including schools, courts, airports, and government offices across multiple states, with reports of such threats emerging in Gujarat over the past year.
The suspect, named Sourav Biswas (30), originally known as Michael Biswas, was taken into custody from the village of Gopalnagar in the North 24 Parganas district of West Bengal. This operation was a collaboration between the Ahmedabad Cyber Crime Branch and the Crime Branch.
Authorities indicated that the suspect entered India during the Covid-19 pandemic in 2021 and has been living illegally in West Bengal since then.
Following his arrest, he was brought to Ahmedabad under transit remand and presented to a court, which granted law enforcement a 10-day police custody period for interrogation.
This arrest is a result of investigations into a series of alarming emails that included threats of bomb explosions directed at schools, courts, airports, post offices, and other governmental entities.
Ahmedabad has seen several of these threats, with similar messages reported in Surat, Vadodara, and Rajkot, as well as in other states, including Delhi, Punjab, Maharashtra, Assam, and Uttar Pradesh.
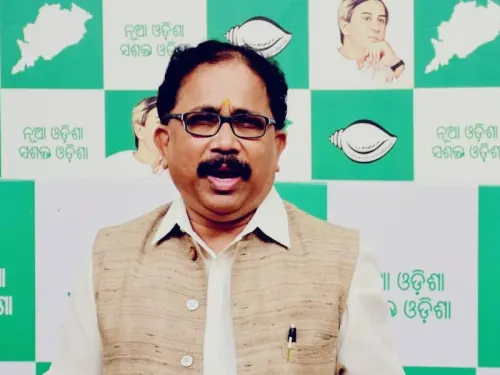
Joint Commissioner of Police (Crime Branch) Sharad Singhal stated that these threats have been circulating for nearly a year and are part of a broader cyber terror investigation.
"For almost a year, bomb threat emails targeting educational institutions and other facilities have been received in Gujarat. Some messages have referenced Khalistan sympathizers, while others highlighted political matters linked to Tamil Nadu. During our investigation, we detained this individual from West Bengal," explained Joint CP Singhal.
He further noted that the Ahmedabad Police Crime Branch secured a swift transit remand, allowing the Cyber Crime team to commence questioning the suspect.
"This operation involved a significant collaboration between the Ahmedabad Crime Branch and Cyber Crime unit. The individual responsible for sending bomb threat messages to multiple locations, including Ahmedabad, has been arrested. He is currently in police custody, and further investigations are ongoing as we explore the involvement of other suspects," added the Joint CP.
According to investigators, the suspect was engaged in the illegal sale of digital services and compromised online accounts via digital platforms and the dark web.
Police reported that the suspect utilized hacked or leaked email accounts and social media profiles, modified their details, and sold them through a site called expetseller.shop (F5gitServices).
This website offered a variety of digital services, including Gmail accounts, bank accounts, Cash App accounts, Google Voice numbers, TextNow accounts, VPN and proxy services, premium subscriptions, and social media accounts such as Facebook, Instagram, WhatsApp, and Telegram, along with phone numbers and Remote Desktop Protocol or Virtual Private Server services.
Reportedly, the suspect sold email accounts for prices ranging from one to five dollars each, accepting payments in cryptocurrency.
Investigators revealed that the suspect employed Virtual Private Network services and other advanced technical tools to obscure identities and track inactive or compromised email accounts.
Upon gaining control of these accounts by altering usernames, passwords, and recovery information, the credentials were allegedly transferred to handlers believed to be operating out of Bangladesh, who then used them to dispatch bomb threat emails.
Approximately 50 to 60 email IDs were reportedly utilized in these threatening communications, with the suspect allegedly receiving around 50 USDT in cryptocurrency for each account provided.
The financial transactions involving USDT are currently under scrutiny.
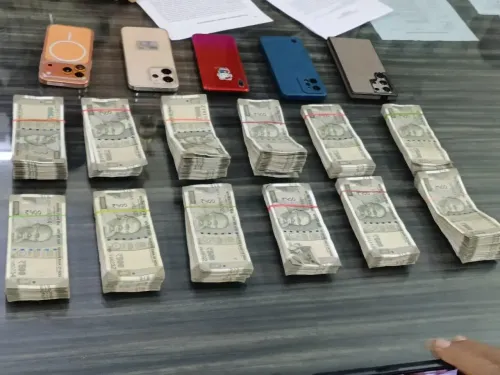
During searches at the suspect's residence, law enforcement seized three CPUs, five computer hard drives, three mobile devices, and an internet router.
Investigators also discovered data containing about 200 Gmail IDs along with their passwords and recovery email details, in addition to several Hotmail accounts believed to have been used in the threat emails.
Officials noted that the suspect had previously worked at a cybercafe before transitioning into digital marketing and online service sales.
"He (the suspect) resided in the largest house in his neighborhood, which is under investigation as part of the financial inquiries," officials remarked.
The investigation has connected the suspect to at least seven cases reported in Ahmedabad between December 2025 and February 2026, with additional incidents in Surat, Vadodara, and Rajkot also being reviewed.
Police conducted a covert operation via Telegram, where officers contacted the suspect and transferred cryptocurrency during a controlled interaction.
After a bomb threat message was later sent to a location in Maharashtra, investigators were able to trace the digital footprint and identify the suspect.
Authorities have indicated that police teams from Delhi, Maharashtra, Punjab, and Uttar Pradesh, in collaboration with central agencies, are expected to arrive in Ahmedabad to interrogate the suspect regarding similar incidents reported in their regions.
Joint CP Singhal stated that investigators are also looking into possible connections with other modules.
"We are investigating the broader network behind these emails, including handlers operating internationally. The involvement of other associates is also being examined," he added.
Police indicated that the suspect's sister, Sarista Biswas, might also have participated in these activities, and further inquiries are ongoing.
Investigators are additionally looking into a suspected module linked to Chennai, although officials maintain that the IP trails observed thus far appear distinct.
The charges have been filed under Sections 351(3), 351(4), 353(1)(B), 61(2) of the Bharatiya Nyaya Sanhita-2023 and Section 66(C) of the IT Act.
Since hacked email accounts were utilized for these criminal activities, additional charges under Sections 43, along with 66, 66(C), and 66F(2) of the IT Act-2000, have been appended to the case.
Authorities confirmed that the investigation is ongoing as officials analyze digital evidence, cryptocurrency transactions, and potential cross-border connections related to the case.