Major Cyber Fraud: Sri Lanka Loses $2.5M in Government Heist

Synopsis
Key Takeaways
Colombo, April 24 — Sri Lanka has launched a sweeping multi-agency investigation after sophisticated cyber fraudsters illegally diverted a government payment of $2.5 million USD that was originally destined for an Australian creditor. The Ministry of Finance confirmed the breach, marking one of the most serious cybersecurity failures in the island nation's recent financial history. The incident has sent shockwaves through Sri Lanka's debt restructuring process at a particularly sensitive moment.
How the Cyber Attack Unfolded
According to the Ministry of Finance, the cybercriminals gained unauthorised access to the computer systems of the External Resources Department (ERD) through a targeted email-based intrusion — a method consistent with Business Email Compromise (BEC), one of the most financially damaging forms of cybercrime globally.
Once inside the system, the attackers manipulated account details and redirected the $2.5 million payment away from the legitimate Australian creditor. The fraud was not immediately detected, highlighting critical gaps in the government's cybersecurity protocols.
The breach came to light when Treasury officials noticed suspicious changes to account details during a separate payment process linked to India. The timely detection prevented an additional fraudulent transaction from being executed, potentially saving further public funds.
Government Response and Internal Action
Treasury Secretary Harshana Suriyapperuma stated that swift intervention by officials allowed authorities to expose the fraud while keeping ongoing investigations intact. He confirmed that an internal committee — comprising senior officials including two Deputy Treasury Secretaries — has been constituted to recommend corrective measures and systemic reforms.
Disciplinary proceedings have been initiated against officials found responsible for procedural lapses that allowed the breach to occur. This signals that the government is treating internal negligence as seriously as the external cyberattack itself.
Sri Lankan authorities have formally notified the Australian government, relevant creditor institutions, and all stakeholders involved in Sri Lanka's ongoing debt restructuring process. Debt analysts have reassured that this incident does not compromise Sri Lanka's sovereign debt obligations.
Australia's Role and International Coordination
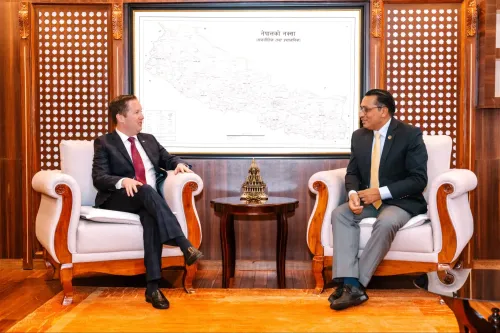
The Australian High Commission confirmed it is coordinating closely with Sri Lankan authorities and remains committed to supporting the country's path toward debt sustainability. The bilateral cooperation underscores the cross-border nature of the cybercrime and the need for international financial security frameworks.
Sri Lankan and international investigators are now jointly working to trace the diverted funds and identify the individuals or groups behind the attack. Given the sophistication of the breach, cybersecurity experts suspect the involvement of organised cybercrime networks with experience in targeting government financial systems.
Broader Implications for Sri Lanka's Financial Security
This incident arrives at a deeply vulnerable moment for Sri Lanka, which is still recovering from its worst economic crisis in decades — a meltdown that led to the country defaulting on its external debt in 2022 and seeking an IMF bailout. The diversion of $2.5 million from a creditor repayment fund is not just a cybercrime — it is a direct threat to the credibility of Sri Lanka's debt restructuring narrative.
Notably, Business Email Compromise (BEC) attacks have cost governments and corporations globally over $50 billion since 2013, according to the FBI's Internet Crime Complaint Center (IC3). Sri Lanka's case fits a well-documented pattern of cybercriminals specifically targeting nations undergoing financial distress, where oversight mechanisms may be stretched thin.
Critics argue that the breach exposes a dangerous gap in Sri Lanka's digital infrastructure for financial governance — a gap that must be urgently addressed if the country is to rebuild international creditor confidence. The incident also raises questions about whether multi-factor authentication and payment verification protocols were in place at the External Resources Department.
What Happens Next
The internal committee is expected to submit its recommendations shortly, which will likely include mandatory cybersecurity audits across all financial ministries and the introduction of stricter payment verification procedures. The government's response in the coming weeks will be closely watched by IMF officials, international creditors, and bilateral partners.
As Sri Lanka continues to navigate its debt restructuring journey, ensuring the integrity of its financial systems is no longer just a governance issue — it is a matter of national economic security. The outcome of this investigation could set a precedent for how South Asian governments respond to state-level cyber financial crimes.