Delhi Police arrest sextortion kingpin Abas Khan from Mewat, recover ₹2.52 lakh fraud

Synopsis
Key Takeaways
Delhi Police's North-West district cyber unit on Wednesday arrested Abas Khan, 25, identified as the alleged kingpin of a sextortion racket operating from the Mewat region in Rajasthan's Alwar district. The breakthrough came after a detailed investigation into cyber fraud involving extortion of ₹2.52 lakh from a Shalimar Bagh resident.
How the sextortion scheme operated
The victim reported receiving a Facebook friend request from a woman's profile, who later obtained his mobile number. During a subsequent WhatsApp video call, obscene content was played while the victim was recorded without his knowledge. The accused then threatened to release the purported video publicly unless the victim paid money. Under duress, the victim transferred ₹2.52 lakh across multiple transactions.
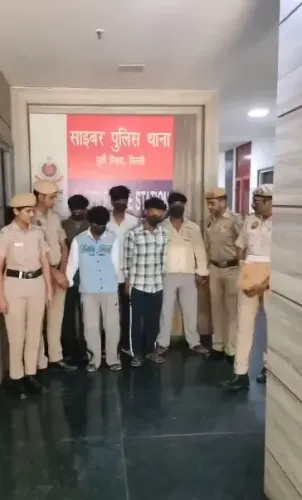
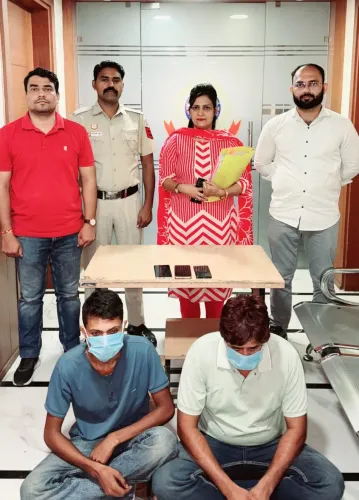
Investigation and arrest
An electronic First Information Report (e-FIR) was registered on 12 January under relevant sections of the Bharatiya Nyaya Sanhita. Police analysed digital footprints including WhatsApp account data, Facebook profiles, Internet Protocol Detail Records (IPDRs), Call Detail Records (CDRs), and bank transactions. The investigation revealed multiple accounts operated through mule identities. Technical surveillance and ground intelligence eventually traced the operation to the Mewat region. A carefully coordinated raid was conducted in the early hours, and Khan was arrested. Police recovered an iPhone 14 Pro allegedly used in the crime.
Modus operandi uncovered
During interrogation, Khan confessed to creating fake social media profiles using photographs of women and sending bulk friend requests to target men. Once a victim engaged, he would initiate a video call and play pre-recorded obscene clips while secretly recording the victim's reaction. These recordings were weaponised to blackmail victims into payments.
Larger network suspected
Police indicated that Khan was a key operator within a broader sextortion network, with further investigation underway to identify and arrest other members. Officials noted that several youths from the accused's village are suspected to be involved in similar cyber fraud activities, suggesting an organised racket spanning multiple operatives.
What's next
The investigation continues as police work to dismantle the wider network. Authorities are also examining whether other victims exist and coordinating with cyber units in adjacent states to track related cases.